Active exploitation of vulnerabilities demands faster patching. Learn to prioritize remediations based on real-world risks across platforms such as Drupal and Ubiquiti UniFi OS.
Read Article - Prioritizing Exploited Vulnerabilities And Patch Strategy Across Critical Platforms

Cybersecurity Insights
Stay informed with articles on risk management, cybersecurity trends, best practices, and actionable advice to help your business protect its digital assets and maintain a strong security posture.
ALL
Business ContinuityComplianceCybersecurityDisaster RecoveryRisk ManagementSecurityStrategyTrainingvCISOVulnerability Management

Posted inBusiness Continuity Compliance Cybersecurity Risk Management Security Vulnerability Management
Managing Critical Infrastructure Vulnerabilities Across Security And Network Platforms
As enterprise networks grow more complex, vulnerabilities in critical infrastructure products like FortiSandbox, SD-WAN controllers, and Exchange servers pose significant risks. This article outlines...
Read Article - Managing Critical Infrastructure Vulnerabilities Across Security And Network Platforms

Turning Security Advisories Into Action Across Critical Systems
Explore practical steps to translate recent security advisories for industrial control systems, PAN-OS firewalls and MOVEit Automation into prioritized patching, configuration and monitoring actions.
Read Article - Turning Security Advisories Into Action Across Critical Systems
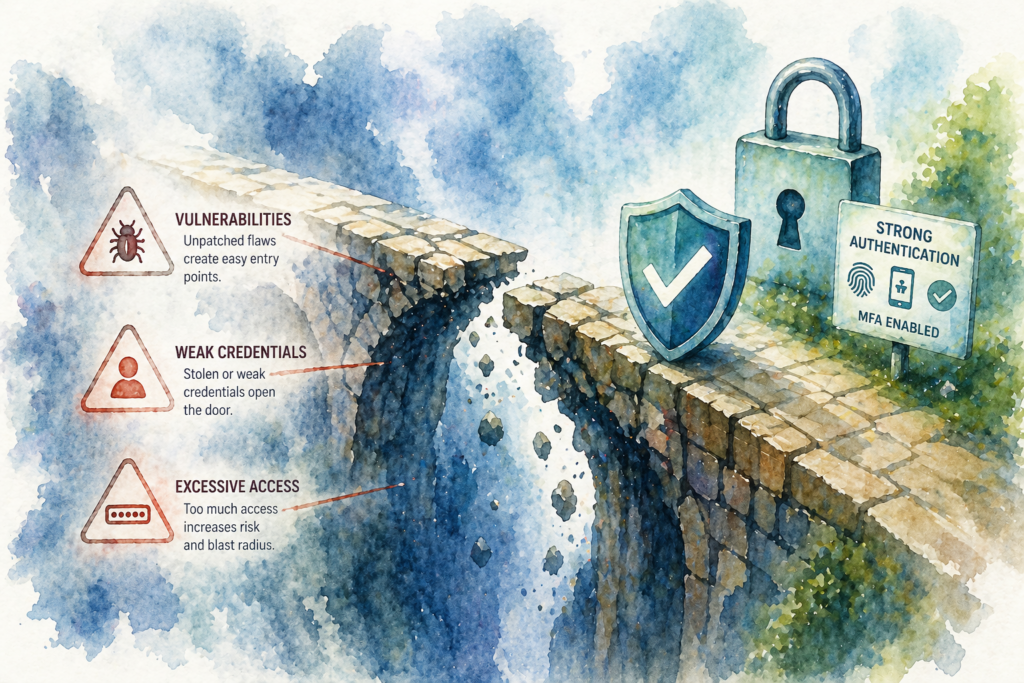
Closing the Gaps Before Attackers Do: Managing Vulnerabilities and Authentication Risks
This article examines three security challenges—critical remote code execution flaws, cPanel authentication bypasses, and upcoming legacy TLS deprecation—and offers actionable steps to mitigate them...
Read Article - Closing the Gaps Before Attackers Do: Managing Vulnerabilities and Authentication Risks

Strengthening Network Defenses: Key Lessons from Recent Critical Vulnerabilities
This post examines critical vulnerabilities in SD-WAN controllers, Ivanti Connect Secure implants, and Juniper PTX routers. It outlines remediation steps—patching, access controls, and monitoring—to...
Read Article - Strengthening Network Defenses: Key Lessons from Recent Critical Vulnerabilities
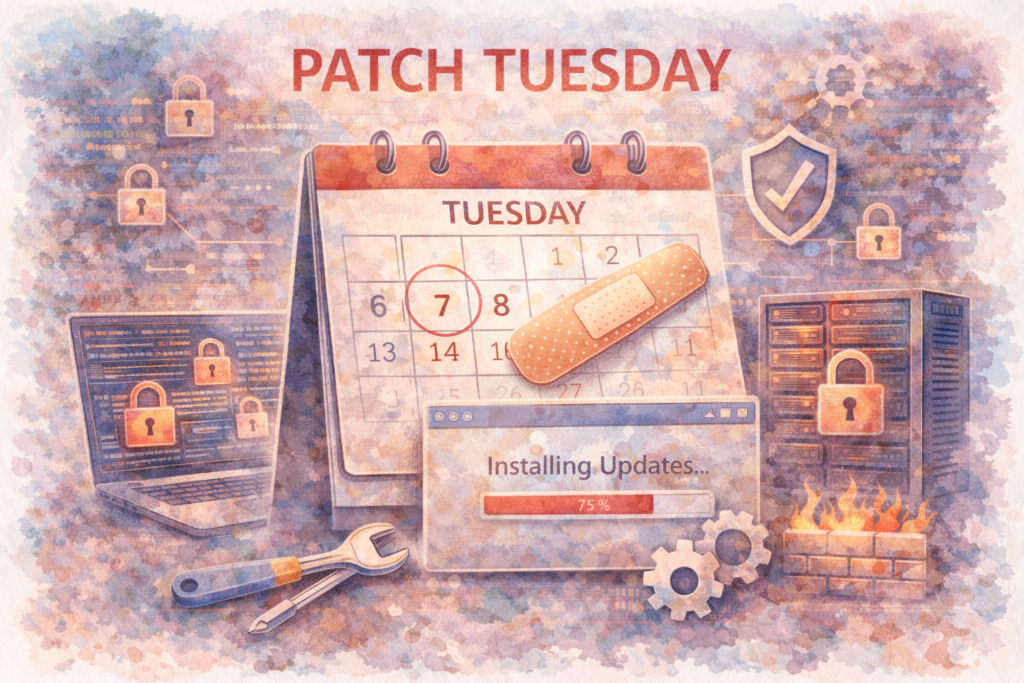
Managing Critical Vulnerabilities: Microsoft Zero-Days, Fortinet EMS, and SolarWinds WHD Exploits
Organizations face a surge of high-severity vulnerabilities in Microsoft, Fortinet EMS, and SolarWinds WHD. This article details agile patch management, network hardening, and proactive...
Read Article - Managing Critical Vulnerabilities: Microsoft Zero-Days, Fortinet EMS, and SolarWinds WHD Exploits

Mitigating Critical Software and Network Vulnerabilities: Office Zero-Day, BGP Route Leaks, and Telnet Exposures
Active Office zero-day attacks, BGP route leaks, and Telnet authentication vulnerabilities expose critical network and software risks. Proactive patch management, rigorous configuration controls, and...
Read Article - Mitigating Critical Software and Network Vulnerabilities: Office Zero-Day, BGP Route Leaks, and Telnet Exposures

Essential Security Alerts: Active Exploits, Legacy Vulnerabilities, and App Reliability
Explore active enterprise software exploits, a legacy telnetd bypass, and mobile app failures, and learn why vulnerability management, patching, and testing are critical.
Read Article - Essential Security Alerts: Active Exploits, Legacy Vulnerabilities, and App Reliability

Strengthening Cyber Resilience: Managing Breach Narratives, VPN Risks, and End-of-Life Devices
This guide provides practical steps to proactively defend against supply-chain breaches, secure VPN gateways from DoS attacks, and mitigate vulnerabilities in end-of-life devices to...
Read Article - Strengthening Cyber Resilience: Managing Breach Narratives, VPN Risks, and End-of-Life Devices

Lessons from Recent Breaches
Recent high-profile breaches reveal that mature systems and trusted partners aren't enough. Business and IT leaders must reinforce defenses through zero-trust, strict controls and...
Read Article - Lessons from Recent Breaches

