Closing the Gaps Before Attackers Do: Managing Vulnerabilities and Authentication Risks
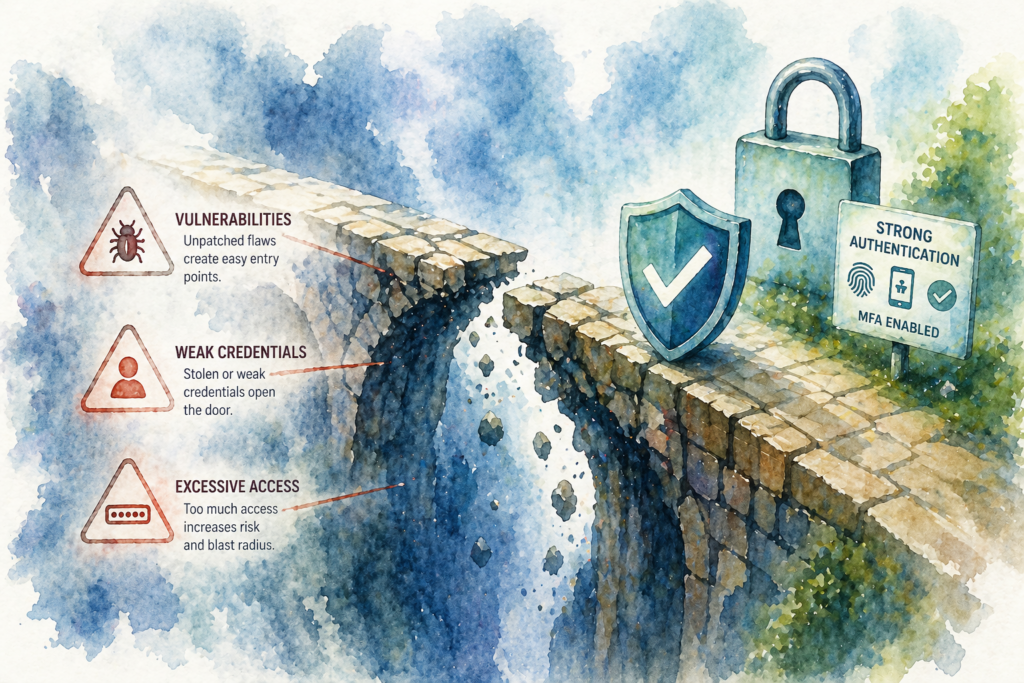
In today’s dynamic threat landscape, organizations face a spectrum of challenges from remote code execution flaws in web frameworks to bypassable control panels and impending protocol changes in cloud email services. Staying ahead requires a disciplined approach to vulnerability management, access controls, and configuration hygiene. This article examines three recent security developments and outlines the steps you can take now to reduce risk, maintain uptime, and safeguard critical assets.
Critical Remote Code Execution Flaws in Web Frameworks and Managed File Transfer
A recent advisory from CISA highlights critical vulnerabilities in components such as ThinkPHP and ELBA5 that allow attackers to run code remotely. Once an exposed service falls victim to successful exploitation, attackers can disrupt operations, access sensitive data, implant persistence mechanisms, or pivot deeper into the network. The advisory also flags an authentication weakness in Fortra GoAnywhere MFT’s SSH key-based access. Even key-based systems can collapse under repeated login attempts if rate limiting and brute-force protections are insufficient.
To manage exposure, start by inventorying all internet-facing and widely deployed internal instances of affected components. Prioritize patching or upgrading those with known flaws, and implement compensating controls, restrict access with network segmentation, enforce strong monitoring of authentication events, and apply web application firewalls where applicable. Regularly validate that rate-limit policies are active and test them under simulated attack conditions. By combining timely remediation with layered defenses, you close off common attack paths and limit an adversary’s ability to leverage a single foothold into a larger breach.
Authentication Bypass in cPanel and WHM Control Panels
An emergency update for cPanel and WHM was released after disclosure of an authentication bypass vulnerability in the control-panel interface. An attacker who reaches this interface may skip normal login procedures and gain direct administrative access. Since cPanel and WHM serve as a central hub for server configuration, covering firewall rules, user-account management, database provisioning, and more. Unauthorized entry can quickly lead to full compromise of hosted services, data exfiltration, or the establishment of persistent backdoors.
To mitigate this risk, apply the vendor’s emergency update on all affected releases without delay. After updating, conduct thorough tests of authentication workflows to confirm that login restrictions have been fully restored. In environments with limited maintenance windows, consider staggered deployments to minimize service interruption. Beyond patching, institute routine access-control reviews and simulate bypass scenarios during scheduled security exercises. These checks ensure that, once a fix is in place, it remains effective even as control-panel configurations evolve over time.
Preparing for Legacy TLS Deprecation in Exchange Online
Microsoft plans to deprecate legacy TLS for POP and IMAP in Exchange Online beginning July 2026. Any client or appliance relying on outdated protocol versions will no longer connect to hosted mail services once this change takes effect. This industry-wide shift reflects the need to retire cipher suites and transport methods deemed insufficient against modern threats.
Avoid disruption by conducting a comprehensive inventory of all systems that use POP or IMAP legacy email clients, on-premises mail appliances, custom reporting tools, and embedded devices with hard-coded interfaces. Engage stakeholders early to map each use case and verify compatibility with current TLS configurations. Schedule updates to client software, apply modern cipher suites, and adjust authentication settings well before the cutoff date. While detailed migration guidance is forthcoming, starting asset discovery and stakeholder communication now will help you align with best practices and maintain uninterrupted mail operations.
Conclusion
These three scenarios: remote code execution in web components, control-panel authentication bypasses, and the impending TLS deprecation underscore the importance of continuous vulnerability management, robust access controls, and proactive configuration reviews. By maintaining an accurate inventory of your assets, applying patches quickly, and validating defenses through testing, you reduce the window of opportunity for attackers and strengthen resilience against emerging threats.
Yobihouse helps organizations stay secure and compliant through high-level vulnerability assessments, configuration reviews, and continuous monitoring services. By aligning security practices with evolving standards and providing strategic guidance on patch management, access controls, and protocol upgrades, Yobihouse supports teams in building and maintaining a robust security posture. Whether you need an independent review of critical infrastructure or assistance in mapping dependencies ahead of major platform changes, Yobihouse can offer the insights and frameworks necessary to improve clarity and readiness.